Massive IoT and 5G: What’s Next for Large-Scale Cellular IoT
November 25, 2025
November 25, 2025
Estimated reading time: 3 minutes
The Internet of Things (IoT) continues to evolve with advancements in LTE and 5G, enabling efficient and scalable connectivity. These networks support a wide range of use cases with:
IoT applications fall into two functional categories:

These applications demand ultrareliable low-latency connectivity for bandwidth-intensive and fault-sensitive use cases. Examples include:

This category encompasses billions of devices transmitting small data packets efficiently. It supports large-scale deployments across:
According to the “Cellular IoT Module Market Insights: Q2 2025” report by Counterpoint Research, global cellular IoT module shipments are expected to reach 936 million units by 2030. They are expected to grow at a 9.4% CAGR from 2024.
Revenue is projected to more than double, rising from $6.8 billion in 2024 to $15.9 billion by 2030. This growth will be driven by a mix of 5G-enabled modules in applications such as:

Massive IoT offers new developments in connectivity for devices worldwide. However, it will challenge network reliability and security. As more use cases arise, so will more opportunities for invasion of privacy and data theft.
Significant IoT challenges must be addressed on the way to full 5G. Advanced LTE, 5G and future 5G networks require enhanced capabilities to manage increasing data traffic as millions more mobile and IoT devices come online.
Data security must be a priority. The industry will experience more aggressive attacks as bad actors exploit the growing vulnerabilities of IoT networks. Data security will become a competitive differentiator for customers seeking to invest in IoT solutions.
Artificial intelligence (AI), machine learning (ML) and edge computing play vital roles in the design and operation of massive IoT networks. These technologies enable:
Each is essential for managing the complexity and scale of large deployments.

5G Reduced Capability (RedCap) is now commercially activated and launched in:
Its readiness is also promising in Japan and Australia.
The value proposition lies in its ability to deliver cost-effective and power-efficient 5G connectivity for mid-tier IoT applications.
RedCap is entering its commercial deployment phase across:
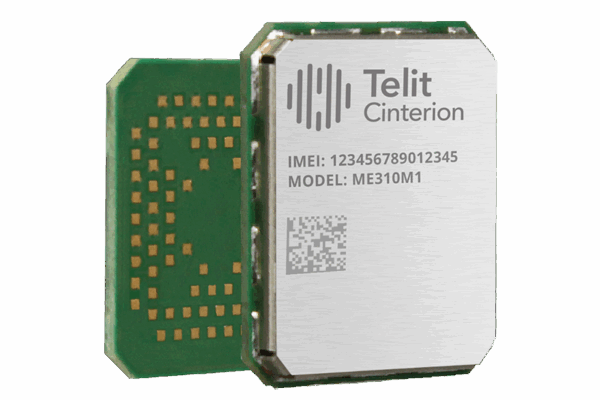
Whether your IoT application falls within massive IoT or critical IoT, our robust cellular 5G data card portfolio has you covered. Speak with our experts to learn which of these modules is best suited for your deployment:
Massive IoT
Critical IoT
Editor’s note: This blog was originally published on 21 September 2020 and has since been updated.