The Best Security Practices for Smart Meters: A Guide
May 28, 2026
Estimated reading time: 7 minutes

Smart meters transform how utilities and consumers interact with energy data. Data generated by smart meters allows utilities and smart grid managers to improve service and efficiency by:
Furnishing this information on energy delivery networks facilitates the integration of Distributed Energy Resources (DERs) and Virtual Power Plants (VPPs).
Smart meters also create new security challenges that cannot be ignored. Like any connected technology, hackers can exploit them. Recent incidents involving gas meters and other smart grid infrastructure show how cybercriminals can exploit firmware weaknesses.
In addition to accessing private consumption data and tampering with readings, cybercriminals can override individual meters, leveraging compromised devices as entry points for lateral movement. This can potentially trigger a cascading failure across the entire grid.

Attack vectors are numerous. Smart meter manufacturers are responsible for securing their products and complying with evolving regulations.
Smart meter manufacturers must analyze supply chain processes to ensure the device is secure and does not expose data. They must also implement measures to prevent supply chain attacks, such as a Robust Hardware Root of Trust (RoT), to ensure the device’s integrity from the factory floor to the field.
Manufacturers should collaborate with vendors that prioritize cybersecurity and can manage connectivity configuration. This includes knowing who can activate or deactivate a device’s iSIM or eSIM credentials.
Figure 1 below shows additional areas smart meter manufacturers must consider, along with corresponding security questions for IoT applications.
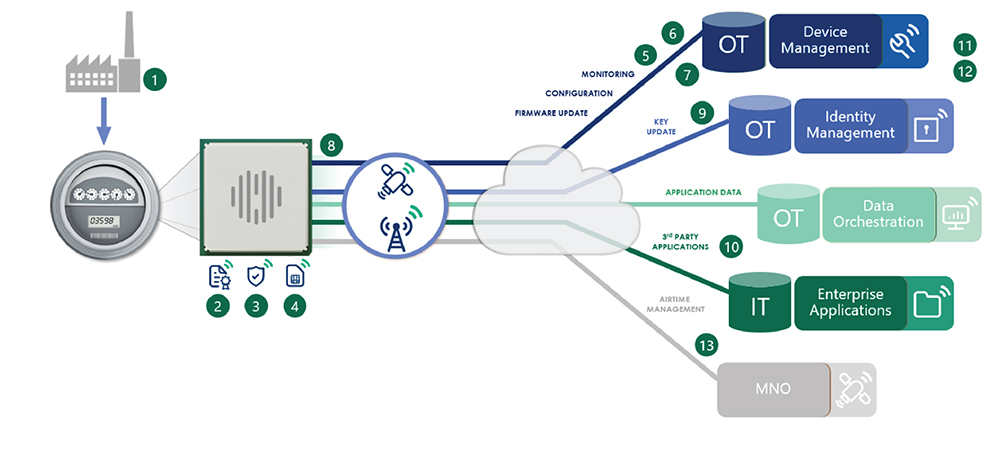
1. Has the device been compromised in manufacturing?
2. Can you trust the code running on the device?
3. Who can access and inspect the device?
4. Where is confidential information stored?
5. Can you update the firmware security patches via secure firmware over-the-air (FOTA) updates?
6. Who can modify device settings?
7. Can you monitor device behavior to detect anomalies in traffic patterns?
8. Can you detect if your device is under attack?
9. Who manages digital identities and credentials?
10. Are the correct authentication and authorization layers for customer data access implemented?
11. Is the platform operated according to best practices and standards (e.g., ISO/IEC 27001 or IEC 62443)?
12. Where is the cloud platform hosted?
13. Who can manage or disable your SIM card?

Advanced metering infrastructure (AMI) is evolving. As it does, smart meters are increasingly having to serve as complex communication devices to complement more sophisticated metrology.
Public key cryptographic schemes are becoming more widespread, building on protocols already used in the IT world. Examples include secure boot and end-to-end encryption. These help defend against man-in-the-middle (MitM) attacks.
The industry is also moving toward Zero Trust architecture (ZTA). With ZTA, every connection request must be authenticated and encrypted regardless of its origin within the network.
Newer technologies are also on the horizon. Quantum computing remains a future threat. The transition to Post-Quantum Cryptography (PQC) standards is already being discussed to ensure 15-year device lifecycles remain resilient against future decryption capabilities.
It is also critical that smart meter manufacturers make their products interoperable. All smart meters will communicate with a head-end system (HES) via a smart metering protocol. The protocol is Device Language Message Specification/Companion Specification for Energy Metering (DLMS/COSEM).
DLMS plays a role in the wider security scheme, specifically through the implementation of Security Suites (such as Suites 1 or 2), which provide authenticated encryption and digital signatures. For a deeper dive into these standards, practitioners should refer to the DLMS User Association technical resources.
The cybersecurity landscape is evolving, with hackers and government-sponsored cybercriminals becoming more sophisticated year after year. To keep pace with bad actors, regulators continue to roll out new standards.
The metering industry is heavily regulated. The European Commission’s Cyber Resilience Act (CRA) now imposes mandatory requirements that address cybersecurity risks in internet-connected radio devices.
The industry is navigating a complex process. Existing harmonized standards must be mapped to the requirements of the Radio Equipment Directive Delegated Regulation (RED-DR). Manufacturers must now provide a Software Bill of Materials (SBOM) to ensure transparency in the software supply chain and rapid vulnerability management.
ESMIG, the European association of smart energy solution providers, plays a key role in representing the meter industry. It addresses regulatory barriers to accelerate practical and attainable green energy transition.
Telit Cinterion works with regulators, policymakers and industry by representing and demonstrating secure, interoperable communications. This is a fundamental requirement for successful metering deployments.

Smart meter deployments can last between 10 and 15 years. Smart meter manufacturers must consider this extended service life when securing their devices. Manufacturers need to partner with a module and service supplier committed to supporting the entire lifecycle and ensuring security.
It’s not just about deploying a device. You are committing to a long-term relationship with that technology partner. An experienced supplier understands its systems aren’t static solutions. This provider will safeguard the product software throughout its lifetime by providing long-term maintenance of the Secure Element (SE) and management of the Public Key Infrastructure (PKI).
Module manufacturers must maintain their modules throughout the smart meter’s life. They can do this by delivering firmware updates that address performance, stability and network configuration. These updates should strengthen security to protect the meter against cyberthreats.
Smart meter manufacturers should prioritize modules that are secure by design. Addressing security issues after deployment is difficult and costly if security is not a core part of the module’s architecture.
When evaluating potential partners, look for vendors with credible backing for their security claims. This will give you confidence that a vendor understands cybersecurity and follows best practices.
Telit Cinterion has helped make smart meters smarter and supported the evolution from automatic meter reading (AMR) to AMI. We have been a trusted partner for global and regional smart meter OEMs. Over the past 30 years, we have successfully connected tens of millions of meters worldwide.
Our approach covers firmware protection and supply chain security. We offer the support you need to keep your smart meter deployments secure throughout their lifecycles. Speak with our smart energy experts to learn more.
Editor’s note: This blog was originally published on 4 April 2024 and has since been updated.